Cyber Security
Protect
Your Business
Long gone are the days when firewalls and anti virus provide adequate data security protection.
The number and complexity of threats today requires a layered approach to security.
Our innovative approach to layered security includes everything from security assessments and multi factor authentication to threat detection, response, and beyond.
Protect your organization’s sensitive assets with the most effective next generation solutions.

Info Solutions’ expertise & knowledge of cyber-security can ensure that your organization is protected from the many threats that exist in today’s world.
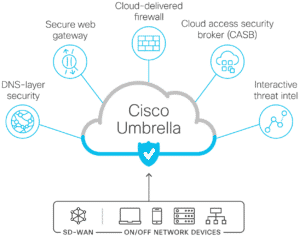
Cisco Umbrella
Cisco Umbrella: Flexible, fast, and effective cloud-delivered security Cisco Umbrella offers flexible, cloud-delivered security when and how you need it. It combines multiple security functions

Two-Factor Authenitcation
Two-Factor Authentication combines something you know, like a password, with something you have, like a cell phone. Watch this video to see how Duo Security

Cyber Security Awareness & Training
Make sure you’re up to date on the latest cyber security threats with our training services!

Security Assessments
Info Solutions offers a full array of Security Assessment Services including a comprehensive portfolio of options to meet all your business security needs. These services

Compliance
Info Solutions offers a wide array of compliance services to help you prepare for, and meet, all your contractual and regulatory compliance obligations. Our international

Strategy & Program Development
Program development is a complex process that requires expertise and experience. When your company needs strategy and program development, turn to our world-class cyber security experts.

Threat Detection & Response
Cyber security threats are increasing exponentially, and attackers are getting sneakier. Cyber attacks are getting more frequent and sophisticated every day. Too often, organizations deal
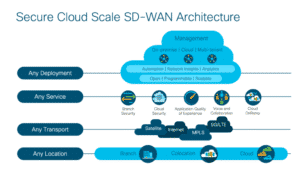
SD-WAN
Software Defined Wide Area Network (SD-WAN) is a cloud-scale architecture designed to meet the complex needs of modern wide area networks through three key areas:

Meraki Managed Services
Managed Meraki Security Simplify security managed by Info Solutions Managing security to protect users and their data is not only essential, but can also be

Firewall Management
Are you currently managing multiple firewalls from different vendors? Do you need help managing the complex details of multiple vendors and layers of protection? If

Application Security
Companies are realizing that the cost of an application security breach is staggering. One study found that a data breach costs a company, on average,

Wireless Security
Protect your business with wireless security. With smart cameras that integrate machine learning and video analysis, identify patterns and problems, and secure your business with

Identity and Access Management
Identity and access management (IAM) is the domain of computing personnel in business, government, education, healthcare, and other enterprise-level IT environments. IAM systems are typically

Data Security
write an excerpt or it will just use the start of the page
